Abstract
In comparison to conventional discrete-variable (DV) quantum key distribution (QKD), continuous-variable (CV) QKD with homodyne/heterodyne measurements has distinct advantages of lower-cost implementation and affinity to wavelength division multiplexing. On the other hand, its continuous nature makes it harder to accommodate to practical signal processing, which is always discretized, leading to lack of complete security proofs so far. Here we propose a tight and robust method of estimating fidelity of an optical pulse to a coherent state via heterodyne measurements. We then construct a binary phase modulated CV-QKD protocol and prove its security in the finite-key-size regime against general coherent attacks, based on proof techniques of DV QKD. Such a complete security proof is indispensable for exploiting the benefits of CV QKD.
Similar content being viewed by others
Introduction
Quantum key distribution (QKD) aims at generating a secret key shared between two remote legitimate parties with information-theoretic security, which provides secure communication against an adversary with arbitrary computational power and hardware technology. Since the first proposal in 19841, various QKD protocols have been proposed with many kinds of encoding and decoding schemes. These protocols are typically classified into two categories depending on the detection methods. One of them is called discrete-variable (DV) QKD, which uses photon detectors and includes earlier protocols such as BB841 and B922 protocols. The other is called continuous-variable (CV) QKD, which uses homodyne and heterodyne measurements with photo detectors3,4,5. See refs. 6,7 for comprehensive reviews of the topic.
Although DV QKD is more mature and achieves a longer distance if photon detectors with low dark count rates are available, CV QKD has its own distinct advantages for a short distance. It can be implemented with components common to coherent optical communication technology and is expected to be cost-effective. Excellent spectral filtering capability inherent in homodyne/heterodyne measurements suppresses crosstalk in wavelength division multiplexing (WDM) channels. This allows multiplexing of hundreds of QKD channels into a single optical fiber8 as well as co-propagation with classical data channels9,10,11,12,13,14,15, which makes integration into existing communication network easier.
One major obstacle in putting CV QKD to practical use is the gap between the employed continuous variables and mandatory digital signal processing. The CV-QKD protocols are divided into two branches depending on whether the modulation method of the encoder is also continuous, or it is discrete. The continuous modulation protocols usually adopts Gaussian modulation, in which the sender chooses the complex amplitude of a coherent-state pulse according to a Gaussian distribution3,4,5,16,17 (see refs. 18,19 for a review). This allows powerful theoretical tools such as Gaussian optimality20,21, and complete security proofs for a finite-size key and against general attacks have been given22. To implement Gaussian protocols with a digital random-number generator and digital signal processing, it is necessary to approximate the continuous distribution with a constellation composed of a large but finite number of complex amplitudes23,24. This is where difficulty arises, and the security analysis has been confined to the asymptotic regime and collective attacks. The other branch gives priority to simplicity of the modulation and uses a very small (usually two to four) number of amplitudes25,26,27,28. As for the security analysis, the status is more or less similar to the Gaussian constellation case, and current security proofs are either in the asymptotic regime against collective attacks29,30,31,32 or in the finite-size regime but against more restrictive attacks33,34. Hence, regardless of approaches, a complete security proof of CV QKD in the finite-size regime against general attacks has been a crucial step yet to be achieved.
Here we achieve the above step by proposing a binary phase-modulated CV-QKD protocol with a complete security proof in the finite-size regime against general attacks. The key ingredient is an estimation method using heterodyne measurement developed in this paper, which is suited for analysis of confidence region in the finite-size regime. The outcome of heterodyne measurement, which is unbounded, is converted to a bounded value by a smooth function such that its expectation is proved to be no larger than the fidelity of the input pulse to a coherent state. This allows us to use a standard technique to derive a lower bound on the fidelity with a required confidence level in the finite-size regime. The fidelity as a measure of disturbance in the binary modulated protocol is essentially the same as what is monitored through bit errors in the B92 protocol2,35,36. This allows us to construct a security proof based on a reduction to distillation of entangled qubit pairs37,38, which is a technique frequently used for DV-QKD protocols.
Results
Estimation of fidelity to a coherent state
We first introduce a test scheme to estimate the fidelity between an optical state ρ and the vacuum state \(\left|0\right\rangle \,\left\langle 0\right|\) through a heterodyne measurement. For a state ρ of a single optical mode, the heterodyne measurement produces an outcome \(\hat{\omega }\in {\mathbb{C}}\) with a probability density
where a coherent state \(\left|\omega \right\rangle\) is defined as
We refer to the expectation associated with the distribution qρ(ω) simply as \({{\mathbb{E}}}_{\rho }\). To construct a lower bound for the fidelity \(\left\langle 0\right|\rho \left|0\right\rangle\) from \(\hat{\omega }\), we will use the associated Laguerre polynomials which are given by
where
are the Laguerre polynomials. Our test scheme is based on the following theorem.
Theorem 1: Let Λm,r(ν) (ν ≥ 0) be a bounded function given by
for an integer m ≥ 0 and a real number r > 0. Then, we have
where In,m are constants satisfying (−1)mIn,m > 0.
From Eq. (6), a lower bound on the fidelity between ρ and the vacuum state is given by
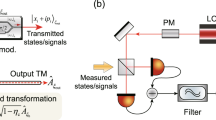
for any odd integer m. As seen in Fig. 1a, the absolute value and the slope of the function Λm,r are moderate for small values of m and r, which is advantageous in executing the test in a finite duration with a finite resolution. Compared to a similar method proposed in ref. 39, our method excels in its tightness for weak input signals; we see from Eq. (6) that, regardless of the value of r, the inequality (7) saturates when ρ has at most m photons. This is crucial for the use in QKD in which tightness directly affects the efficiency of the key generation.
a Example of the test functions Λm,r used in the estimation. The values of r in the figure are chosen so that the range of Λm,r is minimized for given m. In general, the minimum range of the function Λm,r becomes larger as m increases. The pair (m, r) = (1, 0.4120) was used in the numerical simulation of key rates below. b A schematic description of the usage of obtained outcomes in heterodyne measurement. In order to estimate the lower bound on the fidelity to the coherent states \(\left|\pm \beta \right\rangle\), the squared distance between the outcome \(\hat{\omega }\) and the objective point (−1)aβ (i.e., \(| \hat{\omega }-{(-1)}^{a}\beta {| }^{2}\)) is used.
Extension to the fidelity to a coherent state \(\left|\beta \right\rangle\) is straightforward as
The proofs are given in Methods.
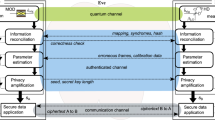
Proposed protocol
Based on this fidelity test, we propose the following discrete-modulation protocol (see Fig. 2). Prior to the protocol, Alice and Bob determine the number of rounds N, the acceptance probability of homodyne measurement \({f}_{{\rm{suc}}}(| x| )\,(x\in {\mathbb{R}})\) with fsuc(0) = 0, the parameters for the test function (m, r), and the protocol parameters (μ, psig, ptest, ptrash, β, s) with psig + ptest + ptrash = 1, where all the parameters are positive. Alice and Bob then run the protocol described in Box 1. Upon successful verification, the protocol generates a shared final key of length
where \(h(x):= -x\,{\mathrm{log}\,}_{2}(x)-(1-x){\mathrm{log}\,}_{2}(1-x)\) is the binary entropy function and the function \(U(\hat{F},{\hat{N}}^{{\rm{trash}}})\) will be specified later.
Alice generates a random bit a ∈ {0, 1} and sends a coherent state with amplitude \({(-1)}^{a}\sqrt{\mu }\). Bob chooses one of the three measurements based on the predetermined probability. In the signal round, Bob performs a homodyne measurement on the received optical pulse and obtains an outcome \(\hat{x}\). In the test round, Bob performs a heterodyne measurement on the received optical pulse and obtains an outcome \(\hat{\omega }\). In the trash round, he produces no outcome.
The acceptance probability fsuc(∣x∣) should be chosen to post-select the rounds with larger values of ∣x∣, for which the bit error probability is expected to be lower. It is ideally a step function, but our security proof is applicable to any form of fsuc(∣x∣). The parameter β is typically chosen to be \(\sqrt{\eta \mu }\) with η being a nominal transmissivity of the quantum channel, while the security proof itself holds for any choice of β. The parameters s and \(s^{\prime}\) are related to the overall security parameter in the security proof below.
Security proof
We determine a sufficient amount of the privacy amplification according to Shor and Preskill37,40, which has been widely used for the DV-QKD protocols. We consider a coherent version of Steps 1 and 2, in which Alice and Bob share an entangled pair of qubits for each success signal round, such that their Z-basis measurement outcomes correspond to the sifted key bits a and b. For Alice, we introduce a qubit A and assume that she entangles it with an optical pulse \(\tilde{C}\) in a state
Then, Step 1 is equivalent to the preparation of \({\left|\Psi \right\rangle }_{A\tilde{C}}\) followed by a measurement of the qubit A on Z basis \(\{\left|0\right\rangle ,\left|1\right\rangle \}\) to determine the bit value a. For Bob, we construct a process of probabilistically converting the received optical pulse C to a qubit B (See Fig. 3). Consider a completely positive (CP) map defined by
with
where \(\left\langle x\right|\) maps a state vector to the value of its wave function at x (See also Eq. (111)). When the pulse C is in a state ρC, the corresponding process succeeds with a probability psuc and then prepares the qubit B in a state ρB, where \({p}_{{\rm{suc}}}{\rho }_{B}={{\mathcal{F}}}_{C\to B}({\rho }_{C})\). If the qubit B is further measured on Z basis, probabilities of the outcome b = 0, 1 are given by
which shows the equivalence to the signal round in Step 2. This is illustrated in Fig. 3.
Bob performs on the optical pulse a non-demolition projective measurement, with which the absolute value of the outcome of homodyne measurement \(| \hat{x}|\) is determined. Then, Bob extracts a qubit B by the operation \({\mathcal{F}}\) defined in Eq. (11). A Z-basis measurement on this qubit gives the same sifted key bit b as described in the actual protocol. On the other hand, the X-basis measurement on this qubit reveals the parity of photon number of the received optical pulse.
To clarify the above observation, we introduce an entanglement-sharing protocol defined in Box 2. This protocol leaves \({\hat{N}}^{{\rm{suc}}}\) pairs of qubits shared by Alice and Bob. If they measure these qubits on Z basis to define the sifted key bits, the whole procedure is equivalent to Steps 1 through 3 of the actual protocol (see Fig. 4). Alice’s measurements on X basis \(\{\left|\pm \right\rangle := (\left|0\right\rangle +\left|1\right\rangle )/\sqrt{2}\}\) in the trash rounds are added for later security argument, and they do not affect the equivalence.
The actual protocol and the estimation protocol are related through the entanglement-sharing protocol. After the entanglement-sharing protocol, Alice and Bob are left with the observed data \(({\hat{N}}^{{\rm{suc}}},{\hat{N}}^{{\rm{fail}}},{\hat{N}}^{{\rm{test}}},{\hat{N}}^{{\rm{trash}}},\hat{F},{\hat{Q}}_{-})\) and \({\hat{N}}^{{\rm{suc}}}\) pairs of qubits. If Alice and Bob ignore \({\hat{Q}}_{-}\) and measure their qubits on the Z-basis to determine their \({\hat{N}}^{{\rm{suc}}}\)-bit sifted keys, it becomes equivalent to the actual protocol. On the other hand, if Alice and Bob measure their \({\hat{N}}^{{\rm{suc}}}\) pairs of qubits on the X-basis, they can count the number \({\hat{N}}_{{\rm{ph}}}^{{\rm{suc}}}\) of phase errors, which we call the estimation protocol. If we can find a reliable upper bound U on \({\hat{N}}_{{\rm{ph}}}^{{\rm{suc}}}\) in the estimation protocol, it restricts the property of the state of \({\hat{N}}^{{\rm{suc}}}\) pairs of qubits after the entanglement-sharing protocol, which in turn limits the amount of leaked information on the sifted keys in the actual protocol. The security proof is thus reduced to finding such an upper bound U in the estimation protocol, represented as a function of the variables that are commonly available in the three protocols.
The Shor-Preskill argument connects the amount of privacy amplification to the so-called phase error rate. Suppose that, after the entanglement-sharing protocol, Alice and Bob measure their \({\hat{N}}^{{\rm{suc}}}\) pairs of qubits on X basis \(\{\left|+\right\rangle ,\left|-\right\rangle \}\). A pair with outcomes (+, −) or (−, +) is defined to be a phase error. Let \({\hat{N}}_{{\rm{ph}}}^{{\rm{suc}}}\) be the number of phase errors among \({\hat{N}}^{{\rm{suc}}}\) pairs. If we can have a good upper bound eph on the phase error rate \({\hat{N}}_{{\rm{ph}}}^{{\rm{suc}}}/{\hat{N}}^{{\rm{suc}}}\), shortening by fraction h(eph) via privacy amplification in the actual protocol achieves the security in the asymptotic limit37.
To cover the finite-size case as well, we need a more rigorous statement on the upper bound. For that purpose, we define an estimation protocol in Box 3 (see also Fig. 4). The task of proving the security of the actual protocol is then reduced to construction of a function \(U(\hat{F},{\hat{N}}^{{\rm{trash}}})\) which satisfies
for any attack in the estimation protocol. It is known that the condition (15) immediately implies that the actual protocol is \({\epsilon }_{\sec }\)-secure with a small security parameter \({\epsilon }_{\sec }=\sqrt{2}\sqrt{\epsilon +{2}^{-s}}+{2}^{-s^{\prime} }\)40,41. See Methods for the rationale and the detailed definition of security.
At this point, it is beneficial for the analysis of the phase error statistics to clarify what property of the optical pulse C is measured by Bob’s X-basis measurement in the estimation protocol (see Fig. 3). Let Πev(od) be the projection to the subspace with even (resp. odd) photon numbers. (Πev + Πod = 1C holds by definition.) Furthermore, since Πev − Πodd is the operator for an optical phase shift of π, we have \(({\Pi }_{{\rm{ev}}}-{\Pi }_{{\rm{odd}}})\left|x\right\rangle =\left|-x\right\rangle\). Eq. (12) is then rewritten as
Therefore, when the state of the pulse C is ρC, the probability of obtaining +(−) in the X-basis measurement in the estimation protocol is given by
where
This shows that Bob’s X-basis measurement distinguishes the parity of the photon number of the received pulse. In this sense, the secrecy of our protocol is assured by the complementarity between the sign of the quadrature and the parity of the photon number.
As an intermediate step toward our final goal of Eq. (15), let us first derive a bound on the expectation value \({\mathbb{E}}[{\hat{N}}_{{\rm{ph}}}^{{\rm{suc}}}]\) in terms of those collected in the test and the trash rounds, \({\mathbb{E}}[\hat{F}]\) and \({\mathbb{E}}[{\hat{Q}}_{-}]\), in the estimation protocol. Let ρAC be the state of the qubit A and the received pulse C averaged over N pairs, and define relevant operators as
Then we immediately have
and
while application of the property of Eq. (8) leads to
Let us denote \({\rm{Tr}}\left({\rho }_{AC}M\right)\) simply by \(\left\langle M\right\rangle\) for any operator M. The set of points \(\big(\big\langle {M}_{{\rm{ph}}}^{{\rm{suc}}}\big\rangle ,\big\langle {\Pi }^{{\rm{fid}}}\big\rangle ,\big\langle {\Pi }_{-}^{{\rm{trash}}}\big\rangle \big)\) for all the density operators ρAC form a convex region. Rather than directly deriving the boundary of the region, it is easier to pursue linear constraints in the form of
where \(B(\kappa ,\gamma ),\kappa ,\gamma \in {\mathbb{R}}\).
It is expected that a meaningful bound is obtained only for κ, γ ≥ 0. Decreasing fidelity \(\left\langle {\Pi }^{{\rm{fid}}}\right\rangle\) should allow more room for eavesdropping, leading to a larger value of phase error rate \(\left\langle {M}_{{\rm{ph}}}^{{\rm{suc}}}\right\rangle\). Hence Eq. (25) will give a good bound only when κ≥0. As for \(\left\langle {\Pi }_{-}^{{\rm{trash}}}\right\rangle\), it only depends on the marginal state of Alice’s qubit A, which is independent of the adversary’s attack. We thus have \(\left\langle {\Pi }_{-}^{{\rm{trash}}}\right\rangle ={q}_{-}:= {\left\Vert {\left\langle -\right|}_{A}{\left|\Psi \right\rangle }_{A\tilde{C}}\right\Vert }^{2}=(1-{e}^{-2\mu })/2\). Since Alice’s use of a stronger pulse should lead to larger leak of information, we should choose γ ≥ 0 for a good bound.
To find a function B(κ, γ) satisfying Eq. (25), let us define an operator
Then Eq. (25) is rewritten as \({\rm{Tr}}\left({\rho }_{AC}M[\kappa ,\gamma ]\right)\le B(\kappa ,\gamma )\). This condition holds for all ρAC iff M[κ, γ] satisfies an operator inequality
If the operator M[κ, γ] was represented by a matrix of a small size, the tightest bound would be found by computing the maximum eigenvalue of the matrix. But here M[κ, γ] has an infinite rank and it is difficult to compute the tightest bound. We thus compromise and heuristically find a computable bound B(κ, γ) which is not necessarily tight; we reduce the problem to finding the maximum eigenvalues of small-size matrices by replacing M[κ, γ] with a constant upper-bound except in a relevant finite-dimensional subspace spanned by \(\left|\pm \beta \right\rangle\) and \({M}_{{\rm{ev}}({\rm{od}})}^{{\rm{suc}}}\left|\pm \beta \right\rangle\). For the detailed derivation of B(κ, γ), see Methods.
With B(κ, γ) computed, we can rewrite Eq. (25) using Eqs. (22)–(24) to obtain a relation between \({\mathbb{E}}[{\hat{N}}_{{\rm{ph}}}^{{\rm{suc}}}]\), \({\mathbb{E}}[\hat{F}]\), and \({\mathbb{E}}[{\hat{Q}}_{-}]\). It is concisely written as
with
This relation leads to an explicit bound on the phase error rate as \({\mathbb{E}}[{\hat{N}}_{{\rm{ph}}}^{{\rm{suc}}}]/{p}_{{\rm{sig}}}N\le B(\kappa ,\gamma )+\gamma {q}_{-}-\kappa \ {\mathbb{E}}[\hat{F}]/{p}_{{\rm{test}}}N\), which is enough for the computation of asymptotic key rates.
The security in the finite-size regime is proved as follows. The fact that the bound given in Eq. (28) is true for all the states ρAC allows us to use Azuma’s inequality42 to evaluate the fluctuations around the expectation value, leading to an inequality
which holds with a probability no smaller than 1 − ϵ/2 (see Methods for the explicit form of δ1(ϵ/2), which is of \(O(\sqrt{N})\)). We remark that the reason for including the trash rounds in the actual protocol is to circumvent a technical issue which would arise in this step. Without measurement of \({\hat{Q}}_{-}\) in the estimation protocol, we would obtain an inequality \({\mathbb{E}}[{p}_{{\rm{sig}}}^{-1}{\hat{N}}_{{\rm{ph}}}^{{\rm{suc}}}+{p}_{{\rm{test}}}^{-1}\kappa \hat{F}]\le NB(\kappa ,\gamma )+\gamma {q}_{-}\). In contrast to Eq. (28), the new inequality is true only when ρAC satisfies \(\left\langle {\Pi }_{-}^{{\rm{trash}}}\right\rangle ={q}_{-}\), which is too stringent for the application of Azuma’s inequality.
Although Eq. (29) includes \({\hat{Q}}_{-}\) which is inaccessible in the actual protocol, we can derive a bound by noticing that it is an outcome from Alice’s qubits and is independent of the adversary’s attack. In fact, given \({\hat{N}}^{{\rm{trash}}}\), it is the tally of \({\hat{N}}^{{\rm{trash}}}\) Bernoulli trials with a probability q−. Hence, we can derive an inequality of the form
which holds with a probability no smaller than 1 − ϵ/2. Here \({\delta }_{2}(\epsilon /2;{\hat{N}}^{{\rm{trash}}})\) can be determined by a Chernoff bound (see Methods). Combining Eqs. (29), (30), and (31), we obtain \(U(\hat{F},{\hat{N}}^{{\rm{trash}}})\) satisfying Eq. (15) to complete the finite-size security proof.
Numerical simulation
We simulated the net key gain per pulse \(\hat{G}\) as a function of attenuation in the optical channel (including the efficiency of Bob’s apparatus). We assume a channel model with a loss with transmissivity η and an excess noise at channel output; Bob receives Gaussian states obtained by randomly displacing coherent states \(\left|\pm \sqrt{\eta \mu }\right\rangle\) to increase their variances by a factor of (1 + ξ)43,44. We assume a step function with a threshold xth( > 0) as the acceptance probability fsuc(∣x∣). The expected amplitude of coherent state β is chosen to be \(\sqrt{\eta \mu }\). We set \({\epsilon }_{\sec }={2}^{-50}\) for the security parameter, and set \(\epsilon ={2}^{-s}={\epsilon }_{\sec }^{2}/16\) and \({2}^{-s^{\prime} }={\epsilon }_{\sec }/2\). We thus have two coefficients (κ, γ), four protocol parameters (μ, xth, psig, ptest), and two parameters (m, r) of the test function to be determined. For each transmissivity η, we determined (κ, γ) via a convex optimization using the CVXPY 1.0.2545,46 and (μ, xth, psig, ptest) via the Nelder-Mead in the scipy.minimize library in Python, in order to maximize the key rate. Furthermore, we adopted m = 1 and r = 0.4120, which leads to \((\max {\Lambda }_{m,r},\min {\Lambda }_{m,r})=(2.824,-0.9932)\). See Methods for the detail of the model of our numerical simulation and examples of optimized parameters. Typical optimized values of the threshold xth range from 0.4 to 1.5 (we adopted a normalization for which the vacuum fluctuation is \(\sqrt{\langle {(\Delta x)}^{2}\rangle }=0.5\)). They are larger than those in other analyses of protocols with post-selection (e.g., ref. 31). A possible reason is the fact that the latter protocols use more than two states to monitor the eavesdropping act, which may lead to a lower cost of privacy amplification and higher tolerance against bit errors.
Figure 5 shows the key rates of our protocol in the asymptotic limit N → ∞ and finite-size cases with N = 109–1012 for ξ = 10−2.0–10−3.0 and 0. (Note that from the results of the recent experiments8,44,47, excess noise with ξ = 10−2.0–10−3.0 at the channel output seems reasonable. Furthermore, the state-of-the-art experiments8 work at 0.5 GHz repetition rate, which implies that total number of rounds N = 109–1012 can be achieved in a realistic duration.) For the noiseless model (ξ = 0), the asymptotic rate reaches 8 dB. In the case of ξ = 10−3.0, it reaches 4 dB, which is comparable to the result of a similar binary modulation protocol proposed in ref. 29. As for finite-size key rates, we see that the noiseless model shows a significant finite-size effect even for N = 1012. On the other hand, with a presence of noises (ξ = 10−3.0) the effect becomes milder, and N = 1011 is enough to achieve a rate close to the asymptotic case. This may be ascribed to the cost of the fidelity test. In order to make sure that the fidelity is no smaller than 1 − δ, the statistical uncertainty of the fidelity test must be reduced to O(δ). As a result, approaching the asymptotic rate of ξ = 0 will require many rounds for the fidelity test.
The abscissa represents attenuation in decibel, i.e., \(-10\,{\mathrm{log}\,}_{10}\eta\). We assumed that the optical pulse that Bob receives is given by randomly displacing a coherent state to increase its variance by a factor of (1 + ξ). a The asymptotic key rate for various values of ξ. b The key rate for various values of ξ when the pulse number is finite (N = 1011). c The key rate without the excess noise (ξ = 0) along with the repeaterless bound (PLOB bound) of the secure key rate in the pure-loss channel55. d The key rate with the excess noise of ξ = 10−3.0.
Discussion
Numerically simulated key rates above were computed on the implicit assumption that Bob’s observed quantities are processed with infinite precision. Even when these are approximated with a finite set of discrete points, we can still prove the security with minimal degradation of key rates. For the heterodyne measurement used for the test in the protocol, assume that a digitized outcome ωdig ensures that the true value \(\hat{\omega }\) lies in a range Ω(ωdig). Then, we need only to replace \({\Lambda }_{m,r}(| \hat{\omega }\pm \beta {| }^{2})\) with its worst-case value, \(\min \{{\Lambda }_{m,r}(| \hat{\omega }\pm \beta {| }^{2}):\hat{\omega }\in \Omega ({\omega }_{{\rm{dig}}})\}\). As seen in Fig. 1a, the slope of function Λm,r(ν) is moderate and goes to zero for ν → ∞. This means that the worst-case value can be made close to the true value, leading to small influence on the key rate. For the homodyne measurement used for the signal, finite precision can be treated through appropriate modification of the acceptance probability fsuc(x). Aside from a very small change in the success rate and the bit error rate, this function affects the key rate only through integrals in Eqs. (116), (118), and (120) in Methods, and hence influence on the key rate is expected to be small. We thus believe that the fundamental obstacles associated with the analog nature of the CV protocol have been settled by our approach.
In comparison with recent asymptotic analyses31,32 of discrete-modulation CV QKD, our protocol achieves lower key rates and much shorter distance. Since ours is the first attempt of applying the proof technique of DV QKD to CV QKD, there is much room for possible improvement. We sacrificed the optimality for simplicity in deriving the operator inequality. The definition of the phase error is not unique and there may be a better choice. The trash rounds were introduced for technical reasons, but we are not sure whether they are really necessary. Nonetheless, we believe that the dominant reason for the difference lies in the fact that our protocol uses only two states. In contrast, the protocols considered in refs. 31,32 use four or more states in signal or test modes. The genuine binary protocol was analyzed in ref. 29, and the key rate derived there is comparable to ours.
In order to improve the presented finite-size key rate, a promising route will thus be increasing the number of states from two. Our fidelity test can be straightforwardly generalized to monitoring of such a larger constellation of signals, and we will be able to confine the adversary’s attacks more tightly than in the present binary protocol. As for the proof techniques to determine the amount of privacy amplification, there are two possible directions. One is to generalize the present DV-QKD-inspired approach of estimating the number of phase errors in qubits to the case of qudits. The other direction is to seek a way to combine the existing analyses31,32,48 of discrete-modulation CV-QKD protocols, which have been reported to yield high key rates in the asymptotic regime, to our fidelity test. Although either of the approaches is nontrivial, we believe that the present results will open up new direction toward exploiting the expected high potential of CV QKD with an improved security level.
In summary, we proved the security of a binary-modulated CV-QKD protocol in the finite-size regime while completely circumventing the problems arising from the analog nature of CV QKD. We believe that it is a significant milestone toward real-world implementation of CV QKD, which has its own advantages.
Methods
Proof of Theorem 1 and Eq. (8)
In this section, we prove Theorem 1 stated in the main text and derive Eq. (8) as a corollary of Theorem 1.
Proof: From Eq. (1), the expectation value of \({\Lambda }_{m,r}(| \hat{\omega }{| }^{2})\) when given a measured state ρ is given by
where
for integers n, m ≥ 0.
The following three properties hold for In,m:
-
(i)
In,m = 0 for m ≥ n ≥ 1.
This results from orthogonality relations of the associated Laguerre polynomials, that is,
Since the polynomial νn−1 can be written as a linear combination of lower order polynomials \({\{{L}_{l}^{(1)}(\nu )\}}_{0\le l\le n-1}\), In,m vanishes whenever m ≥ n ≥ 1.
-
(ii)
(−1)mIn,m > 0 for n > m ≥ 0.
This property is shown as follows. First, the associated Laguerre polynomials satisfy the following recurrence relation for m ≥ 149:
Substituting this to Eq. (33) and using integration by parts, we have
for n ≥ 1 and m ≥ 1. The property (ii) is then proved by induction over m. For m = 0, it is true since In,0 = 1 > 0. When (−1)m−1In,m−1 > 0 for n > m − 1, we can prove (−1)mIn,m > 0 for n > m by using Eq. (36) recursively with Im,m = 0 from property (i).
-
(iii)
I0,m = 1 for m ≥ 0.
This also follows from property (i) and Eq. (36) for n = 1 and m ≥ 1, which leads to I0,m = I0,0 = 1.
Combining properties (i), (ii), and (iii) shows Eq. (6).
Eq. (8) in the main text is derived as the following corollary.
Corollary 1: Let \(\left|\beta \right\rangle\;\)\((\beta \in {\mathbb{C}})\) be the coherent state with amplitude β. Then, for any \(\beta \in {\mathbb{C}}\) and for any odd positive integer m, we have
Proof: From Eq. (6) of Theorem 1, for any odd positive integer m, we have
Let Dβ be a displacement operator satisfying
and \({D}_{\beta }^{\dagger }={D}_{-\beta }\). With \(\tilde{\rho }:= {D}_{\beta }\rho {D}_{\beta }^{\dagger }\), we have \({q}_{\tilde{\rho }}(\omega )={q}_{\rho }(\omega -\beta )\) for probability density function of heterodyne measurement outcome, which implies that
Replacing \(\tilde{\rho }\) with ρ, we obtain Eq. (37).
Detail of the security proof
In this section, we prove the security of the proposed protocol in the main text. This section consists of several subsections. In the first subsection, we give a definition of security, which is standard in the literature. The security condition is divided into two conditions, secrecy and correctness. Since the correctness is trivially satisfied, it is the secrecy that is the focus of the security proof. The second subsection explains how the secrecy condition is reduced to Eq. (15) of the estimation protocol, which bounds the number of phase errors. The third subsection lays the groundwork for the full security proof by deriving the inequality (27) involving three operators relevant for the quantities observed in the signal, the test, and the trash round in the estimation protocol. After proving a general lemma (Lemma 1), an explicit form of the upper bound B(κ, γ) satisfying Eq. (27) is given as a corollary (Corollary 2) of the lemma. Finally, the fourth subsection uses Azuma’s inequality and Corollaries 1 and 2 to derive an explicit form of \(U(\hat{F},{\hat{N}}^{{\rm{trash}}})\) that fulfills Eq. (15), which completes the security proof of the actual protocol.
1. Definition of security in the finite-size regime. We evaluate the secrecy of the final key as follows. When the final key length is Nfin ≥ 1, we represent Alice’s final key and an adversary’s quantum system as a joint state
and define the corresponding ideal state as
Let \({\left\Vert \sigma \right\Vert }_{1}={\rm{Tr}}\sqrt{{\sigma }^{\dagger }\sigma }\) be the trace norm of an operator σ. We say a protocol is ϵsct-secret when
holds regardless of the adversary’s attack. The main goal of the security proof is to derive the amount of privacy amplification, or equivalently to find the function \(U(\hat{F},{\hat{N}}^{{\rm{trash}}})\) in Eq. (9), such that Eq. (43) should hold for given ϵsct > 0.
For correctness, we say a protocol is ϵcor-correct if the probability for Alice’s and Bob’s final key to differ is bounded by ϵcor. Our protocol achieves \({\epsilon }_{{\rm{cor}}}={2}^{-s^{\prime} }\) via the verification in Step 4.
When the above two conditions are met, the protocol becomes \({\epsilon }_{\sec }\)-secure with \({\epsilon }_{\sec }={\epsilon }_{{\rm{sct}}}+{\epsilon }_{{\rm{cor}}}\) in the sense of universal composability50.
2. Reduction to the estimation protocol. Here we show that Eq. (15) in the estimation protocol implies ϵsct-secrecy of the actual protocol with \({\epsilon }_{{\rm{sct}}}=\sqrt{2}\sqrt{\epsilon +{2}^{-s}}\). We have already seen that the entanglement-sharing protocol immediately followed by Z-basis measurements of the qubits is equivalent to Steps 1 through 3 of the actual protocol. Here we consider a slightly modified scenario in which, after the entanglement-sharing protocol, a controlled-NOT operation V is applied on each pair of qubits, where \(V:= \left|0\right\rangle \,{\left\langle 0\right|}_{A}\otimes {{\bf{1}}}_{B}+\left|1\right\rangle \,{\left\langle 1\right|}_{A}\otimes {X}_{B}\) with \({X}_{B}:= \left|1\right\rangle \,{\left\langle 0\right|}_{B}+\left|0\right\rangle \,{\left\langle 1\right|}_{B}\). Alice then measures her qubits on the Z basis to define her sifted key bits and proceeds with Step 5 of the actual protocol. Since V does not affect the Z-basis value of the Alice’s qubit, her procedure of determining the \({\hat{N}}^{{\rm{fin}}}\)-bit final key in this scenario is equivalent to that in the actual protocol. Although V prevents Bob from obtaining an equivalent final key, he can still simulate the reconciliation and the verification process in Step 4 since the Z-basis value of each of his \({\hat{N}}^{{\rm{suc}}}\) qubits corresponds to absence/presence of a bit error between Alice’s and Bob’s sifted key bits. Hence Bob can equivalently carry out all the announcements in Steps 4 and 5 of the actual protocol. As a result, this scenario leads to exactly the same distribution Pr(Nfin) and the same states \({\rho }_{{\rm{AE}}| {N}^{{\rm{fin}}}}^{{\rm{fin}}}\) as those of the actual protocol.
The secrecy of Alice’s final key can be determined from the X-basis property of her \({\hat{N}}^{{\rm{suc}}}\) qubits after the application of V. Since V can be rewritten as \(V={{\bf{1}}}_{A}\otimes \left|+\right\rangle \,{\left\langle +\right|}_{B}+{Z}_{A}\otimes \left|-\right\rangle \,{\left\langle -\right|}_{B}\) with \({Z}_{A}:= \left|-\right\rangle \,{\left\langle +\right|}_{A}+\left|+\right\rangle \,{\left\langle -\right|}_{A}\), the X-basis value of each of Alice’s qubits corresponds to absence/presence of a phase error. Suppose that these \({\hat{N}}^{{\rm{suc}}}\) qubits are measured on the X-basis to produce an outcome \(\hat{{\boldsymbol{x}}}\in {\{+,-\}}^{{\hat{N}}^{{\rm{suc}}}}\). Let \({\rm{wt}}(\hat{{\boldsymbol{x}}})\) be the number of symbol ‘−’ in \(\hat{{\boldsymbol{x}}}\). If Eq. (15) holds in the estimation protocol, the statistics of \(\hat{{\boldsymbol{x}}}\) should satisfy
which implies that the number of probable patterns \(\hat{{\boldsymbol{x}}}\) is limited. To be more precise, let us introduce a set Ω(n, w) ≔ {x ∈ {+, −}n∣ wt(x) ≤ w}, whose size is bounded as ∣Ω(n, w)∣ ≤ 2nh(w/n). The condition (44) then implies
with \({\mathcal{T}}({\hat{N}}^{{\rm{suc}}},\hat{F},{\hat{N}}^{{\rm{trash}}}):= \Omega \left({\hat{N}}^{{\rm{suc}}},U(\hat{F},{\hat{N}}^{{\rm{trash}}})\right)\), which satisfies
from Eq. (9). It is known40,41,51 that the above conditions imply Eq. (43) with \({\epsilon }_{{\rm{sct}}}=\sqrt{2}\sqrt{\epsilon +{2}^{-s}}\). Therefore, it suffices to show that Eq. (15) holds in the estimation protocol for proving the actual protocol to be \({\epsilon }_{\sec }\)-secure with \({\epsilon }_{\sec }=\sqrt{2}\sqrt{\epsilon +{2}^{-s}}+{2}^{-s^{\prime} }\).
We remark that the encryption of \(M:= {H}_{{\rm{EC}}}+s^{\prime}\) bits in Step 4 can be omitted as long as each bit linearly depends on Alice’s sifted key over GF(2). In such a case, the above scenario must include measurements on Alice’s qubits to simulate the announcement of the M bits in Step 4. The backaction on X basis caused by the measurement for each bit amounts to doubling the number of probable patterns \(\hat{{\boldsymbol{x}}}\). We can thus redefine the set \({\mathcal{T}}({\hat{N}}^{{\rm{suc}}},\hat{F},{\hat{N}}^{{\rm{trash}}})\) by enlarging its size by factor of 2M such that Eq. (45) holds. Then, by decreasing \({\hat{N}}^{{\rm{fin}}}\) by M, Eq. (46) also holds. This means that we achieve the same net key rate with the same level of security.
3. Derivation of the operator inequality. The aim of this subsection is to construct B(κ, γ) which fulfills the operator inequality (27). Let \({\sigma }_{\sup }(O)\) denote the supremum of the spectrum of a bounded self-adjoint operator O. Although \(B(\kappa ,\gamma )={\sigma }_{\sup }(M[\kappa ,\gamma ])\) would give the tightest bound satisfying Eq. (27), it is hard to compute it numerically since system C has an infinite-dimensional Hilbert space. Instead, we derive a looser but simpler bound. We first prove the following lemma.
Lemma 1: Let Π± be orthogonal projections satisfying Π+Π− = 0. Suppose that the rank of Π± is no smaller than 2 or infinite. Let M± be self-adjoint operators satisfying Π±M±Π± = M± ≤ α±Π±, where α± are real constants. Let \(\left|\psi \right\rangle\) be an unnormalized vector satisfying \(({\Pi }_{+}+{\Pi }_{-})\left|\psi \right\rangle =\left|\psi \right\rangle\) and \({\Pi }_{\pm }\left|\psi \right\rangle\,\ne\,0\). Define following quantities with respect to \(\left|\psi \right\rangle\):
Then, for any real numbers γ+ and γ−, we have
where four dimensional matrix M4d is defined as
Proof: We choose orthonormal vectors \(\left\{\left|{e}_{\pm }^{(1)}\right\rangle ,\left|{e}_{\pm }^{(2)}\right\rangle \right\}\) in the domain of Π±, respectively, to satisfy
which is well-defined due to Eqs. (47)–(49) and Π±M±Π± = M±. From \(({\Pi }_{+}+{\Pi }_{-})\left|\psi \right\rangle =\left|\psi \right\rangle\), we have
Let us define the following projection operators:
Since Eq. (53) implies \({\Pi }_{\pm }^{(\ge 3)}{M}_{\pm }{\Pi }_{\pm }^{(1)}=0\), we have
The second term in the right-hand side of Eq. (58) is bounded as
since M± ≤ α±Π±. Combining Eqs. (48), (58), and (59), we have
Combining Eqs. (54) and (60), we have
where M4d is given in Eq. (51) with the basis \(\{\big|{e}_{+}^{(2)}\big\rangle ,\big|{e}_{+}^{(1)}\big\rangle ,\big|{e}_{-}^{(1)}\big\rangle ,\big|{e}_{-}^{(2)}\big\rangle \}\). Since \({\alpha }_{\pm }-{\gamma }_{\pm }=\big\langle {e}_{\pm }^{(2)}\big|{M}_{{\rm{4d}}}\big|{e}_{\pm }^{(2)}\big\rangle \le {\sigma }_{\sup }\left({M}_{{\rm{4d}}}\right)\), supremum of the spectrum of the right-hand side of Eq. (61) is equal to the maximum eigenvalue of the four-dimensional matrix M4d. We thus obtain Eq. (50).
As a corollary, we derive Eq. (27) as follows.
Corollary 2: Let \(\left|\beta \right\rangle\) be a coherent state. Let Πev(od), \({M}_{{\rm{ev}}({\rm{od}})}^{{\rm{suc}}}\), and M[κ, γ] be as defined in the main text, and define following quantities:
Let \({M}_{{\rm{4d}}}^{{\rm{err}}}[\kappa ,\gamma ]\) and \({M}_{{\rm{2d}}}^{{\rm{cor}}}[\kappa ,\gamma ]\) be defined as follows:
Define a convex function
Then, for κ, γ ≥ 0, we have
Proof: Let us first observe that the operator Πfid defined in Eq. (20) can be rewritten as follows:
where orthogonal states \({\left|{\phi }_{{\rm{err}}}\right\rangle }_{AC}\) and \({\left|{\phi }_{{\rm{cor}}}\right\rangle }_{AC}\) are defined as
Next, using Eqs. (70), (19), and (21), we rearrange the operator M[κ, γ] defined in Eq. (26) as follows:
where
We can apply Lemma 1 to Merr[κ, γ] by the following substitutions
Here, M± ≤ Π± (i.e., α± = 1) holds because \({M}_{{\rm{od(ev)}}}^{{\rm{suc}}}\) are POVM elements. The other prerequisites of Lemma 1 are easy to be confirmed. Thus, we obtain
In the same way, we can apply Lemma 1 to Mcor[κ, γ] via
Since M± = 0 implies D± = V± = 0 in Lemma 1, this time we can reduce the dimension of relevant matrix Eq. (51) by separating known eigenvalues 0 and −γ. Therefore, we have
where the last inequality holds since γ ≥ 0 and κCev ≥ 0. We then obtain Eq. (69) from Eqs. (73), (81), and (87). Since \({M}_{{\rm{4d}}}^{{\rm{err}}}[\kappa ,\gamma ]\) and \({M}_{{\rm{2d}}}^{{\rm{cor}}}[\kappa ,\gamma ]\) are symmetric and their elements linearly depend on κ and γ, \({\sigma }_{\sup }\left({M}_{{\rm{4d}}}^{{\rm{err}}}[\kappa ,\gamma ]\right)\) and \({\sigma }_{\sup }\left({M}_{{\rm{2d}}}^{{\rm{cor}}}[\kappa ,\gamma ]\right)\) are convex functions over κ and γ, and so is B(κ, γ).
4. Derivation of the finite-size bound. Here we construct the function \(U(\hat{F},{\hat{N}}^{{\rm{trash}}})\) to satisfy Eq. (15) in the estimation protocol. For that, we will first derive Eq. (30). In the estimation protocol, we define the following random variables labeled by the number i of the round;
-
(i)
\({\hat{N}}_{{\rm{ph}}}^{{\rm{suc}},(i)}\) is defined to be unity only when “signal” is chosen in the i-th round, the detection is a “success”, and a pair of outcomes \((a^{\prime} ,b^{\prime} )\) is (+, −) or (−, +). Otherwise, \({\hat{N}}_{{\rm{ph}}}^{{\rm{suc}},(i)}=0\). We have
$${\hat{N}}_{{\rm{ph}}}^{{\rm{suc}},(i)}=\left\{\begin{array}{ll}1&\left({\rm{signal}},\,{\rm{success,}}\,(+,-)\ {\rm{or}}\ (-,+)\right)\\ 0&({\rm{otherwise}}),\hfill\end{array}\right.$$(88)and \({\hat{N}}_{{\rm{ph}}}^{{\rm{suc}}}=\mathop{\sum }\nolimits_{i = 1}^{N}{\hat{N}}_{{\rm{ph}}}^{{\rm{suc}},(i)}\).
-
(ii)
\({\hat{F}}^{(i)}\) is defined to be \({\Lambda }_{m,r}(| \hat{\omega }-{(-1)}^{a}\beta {| }^{2})\) when “test” is chosen in the i-th round. We have
$${\hat{F}}^{(i)}=\left\{\begin{array}{ll}{\Lambda }_{m,r}(| \hat{\omega }-{(-1)}^{a}\beta {| }^{2})&({\rm{test}})\hfill\\ 0\hfill&({\rm{otherwise}}),\end{array}\right.$$(89)and \(\hat{F}=\mathop{\sum }\nolimits_{i = 1}^{N}{\hat{F}}^{(i)}\).
-
(iii)
\({\hat{Q}}_{-}^{(i)}\) is defined to be unity only when “trash” is chosen in the i-th round and \(a^{\prime} =-\). Otherwise, \({\hat{Q}}_{-}^{(i)}=0\). We have
$${\hat{Q}}_{-}^{(i)}=\left\{\begin{array}{ll}1&({\rm{trash}},\,-)\\ 0&({\rm{otherwise}}),\end{array}\right.$$(90)and \({\hat{Q}}_{-}=\mathop{\sum }\nolimits_{i = 1}^{N}{\hat{Q}}_{-}^{(i)}\).
-
(iv)
We also define
$${\hat{T}}^{(i)}:= {p}_{{\rm{sig}}}^{-1}{\hat{N}}_{{\rm{ph}}}^{{\rm{suc}},(i)}+{p}_{{\rm{test}}}^{-1}\kappa {\hat{F}}^{(i)}-{p}_{{\rm{trash}}}^{-1}\gamma {\hat{Q}}_{-}^{(i)},$$(91)which leads to \(\hat{T}[\kappa ,\gamma ]=\mathop{\sum }\nolimits_{i = 1}^{N}{\hat{T}}^{(i)}\).
We will make use of Azuma’s inequality42. We define stochastic processes \({\{{\hat{X}}^{(k)}\}}_{k = 0,\ldots ,N}\) and \({\{{\hat{Y}}^{(k)}\}}_{k = 1,\ldots ,N}\) as follows:
where \({\hat{X}}^{\,{<}\,k}:= ({\hat{X}}^{(0)},{\hat{X}}^{(1)},\ldots ,{\hat{X}}^{(k-1)})\). Note that \({\hat{Y}}^{(k)}\) is a constant when conditioned on \({\hat{X}}^{\,{<}\,k}\). Such a sequence \({\{{\hat{Y}}^{(k)}\}}_{k = 1,2,\ldots }\) is called a predictable process with regards to \(\{{\hat{X}}^{(k)}\}\). Since \({\hat{T}}^{(i)}\) is bounded for any i and \({\{{\hat{X}}^{(k)}\}}_{k = 0,1,\ldots }\) is a martingale, we can apply Azuma’s inequality.
Proposition 1 (Azuma’s inequality52,53): Suppose \({\{{\hat{X}}^{(k)}\}}_{k = 0,1,\ldots }\) is a martingale which satisfies
for constants \({c}_{\min }\) and \({c}_{\max }\), and a predictable process \({\{{\hat{Y}}^{(k)}\}}_{k = 1,2,\ldots }\) with regards to \(\{{\hat{X}}^{(k)}\}\), i.e., \({\hat{Y}}^{(k)}\) is constant when conditioned on \({\hat{X}}^{\,{<}\,k}\). Then, for all positive integers N and all positive reals δ,
We define constants \({c}_{\min }\) and \({c}_{\max }\) as follows. In each round, at most one of \({\hat{N}}_{{\rm{ph}}}^{{\rm{suc}},(i)}\), \({\hat{F}}^{(i)}\), and \({\hat{Q}}_{-}^{(i)}\) takes non-zero value; \({\hat{N}}_{{\rm{ph}}}^{{\rm{suc}},(i)}\) and \({\hat{Q}}_{-}^{(i)}\) are either zero or unity, and \(\min {\Lambda }_{m,r}\le {\hat{F}}^{(i)}\le \max {\Lambda }_{m,r}\). Since κ, γ ≥ 0, Eq. (95) holds when \({c}_{\min }\) and \({c}_{\max }\) are defined as
With \({c}_{\min }\) and \({c}_{\max }\) defined as above, we further define
Setting δ = δ1(ϵ/2) in the proposition, we conclude that
holds with a probability no smaller than 1 − ϵ/2.
Next, we will construct a deterministic bound on \({\hat{Y}}^{(i)}\). Let \({\rho }_{AC}^{(i)}\) be the state of Alice’s i-th qubit and Bob’s i-th pulse conditioned on \({\hat{X}}^{\,{<}\,i}\). Then, using the same argument as that has lead to Eqs. (22)–(24), we have
and thus
where M[κ, γ] is defined in Eq. (26). Using the operator inequality (27), we obtain a bound independent of i as
Combining this with Eq. (100) proves Eq. (30).
The function \({\delta }_{2}(\epsilon /2;{\hat{N}}^{{\rm{trash}}})\) satisfying the bound (31) on \({\hat{Q}}_{-}\) can be derived from the fact that \(\Pr [{\hat{Q}}_{-}| {\hat{N}}^{{\rm{trash}}}]\) is a binomial distribution. The following inequality thus holds for any positive integer n and a real δ with 0 < δ < (1 − q−)n (Chernoff bound):
where
is the Kullback-Leibler divergence. On the other hand, for any non-negative integer n, we always have
Therefore, for any non-negative integer n, by defining δ2(ϵ; n) which satisfies
and by combining Eq. (106) and (108), we conclude that Eq. (31) holds with a probability no smaller than 1 − ϵ/2.
Combining Eq. (30) and Eq. (31), we obtain Eq. (15) by setting
which holds with a probability no smaller than 1 − ϵ (Union bound). Note that since B(κ, γ) is a convex function, so is \(U(\hat{F},{\hat{N}}^{{\rm{trash}}})\) with respect to auxiliary parameters κ and γ.
Models for numerical simulation of key rates
In what follows, we normalize quadrature x such that a coherent state \(\left|\omega \right\rangle\) has expectation \(\left\langle x\right\rangle ={\rm{Re}}(\omega )\) and variance \(\left\langle {(\Delta x)}^{2}\right\rangle =1/4\). The wave function for ω = ωR + iωI is given by
For the simulation of the key rate \(\hat{G}\), we assume that the communication channel and Bob’s detection apparatus can be modeled by a pure loss channel followed by random displacement, that is, the states which Bob receives are given by
where η is the transmissivity of the pure loss channel and pξ(γ) is given by
The parameter ξ is the excess noise relative to the vacuum, namely,
We assume that Bob sets \(\beta =\sqrt{\eta \mu }\) for the fidelity test. The actual fidelity between Bob’s objective state \(\left|{(-1)}^{a}\sqrt{\eta \mu }\right\rangle\) and the model state \({\rho }_{{\rm{model}}}^{(a)}\) is given by
For the acceptance probability of Bob’s measurement in the signal rounds, we assume fsuc(x) = Θ(∣x∣ − xth), a step function with the threshold xth > 0. In this case, the quantities defined in Eqs. (64) and (65) are given by
where \(\beta =\sqrt{\eta \mu }\) and the complementary error function \({\rm{erfc}}(x)\) is defined as
For the derivation of Eq. (120), we used the fact that Πev + Πod = 1 and \(({\Pi }_{{\rm{ev}}}-{\Pi }_{{\rm{od}}})\left|\beta \right\rangle =\left|-\beta \right\rangle\).
We assume that the number of “success” signal rounds \({\hat{N}}^{{\rm{suc}}}\) is equal to its expectation value,
where
We also assume that the number of test rounds \({\hat{N}}^{{\rm{test}}}\) is equal to ptestN and the number of trash rounds \({\hat{N}}^{{\rm{trash}}}\) is equal to ptrashN. The test outcome \(\hat{F}\) is assumed to be equal to its expectation value \({\mathbb{E}}[\hat{F}]\), which is given by
Under these assumptions, the key rate \(\hat{G}\) for each transmissivity η is optimized over two coefficients (κ, γ) and four protocol parameters (μ, xth, psig, ptest) as discussed in the main part. Examples of optimized parameters are shown in Table 1. The cost of bit error correction HEC is assumed to be \(1.1\times {\hat{N}}^{{\rm{suc}}}h({e}_{{\rm{bit}}})\), where the bit error rate ebit is given by
Data availability
Data sharing not applicable to the article as no datasets were generated or analyzed during the current study.
Code availability
Computer codes to calculate the key rates are available from the corresponding author upon reasonable request.
References
Bennett, C. H. & Brassard, G. Quantum cryptography: Public key distribution and coin tossing. In Proceedings of IEEE International Conference on Computers, Systems, and Signal Processing, 175 (India, 1984).
Bennett, C. H. Quantum cryptography using any two nonorthogonal states. Phys. Rev. Lett. 68, 3121 (1992).
Ralph, T. C. Continuous variable quantum cryptography. Phys. Rev. A 61, 010303 (1999).
Hillery, M. Quantum cryptography with squeezed states. Phys. Rev. A 61, 022309 (2000).
Grosshans, F. & Grangier, P. Continuous variable quantum cryptography using coherent states. Phys. Rev. Lett. 88, 057902 (2002).
Xu, F., Ma, X., Zhang, Q., Lo, H.-K. & Pan, J.-W. Secure quantum key distribution with realistic devices. Rev. Mod. Phys. 92, 025002 (2020).
Pirandola, S. et al. Advances in quantum cryptography. Preprint at https://arxiv.org/abs/1906.01645 (2019).
Eriksson, T. A. et al. Wavelength division multiplexing of 194 continuous variable quantum key distribution channels. J. Lightwave Technol. 38, 2214–2218 (2020).
Huang, D. et al. Continuous-variable quantum key distribution with 1 Mbps secure key rate. Opt. Express 23, 17511–17519 (2015).
Kumar, R., Qin, H. & Alléaume, R. Coexistence of continuous variable QKD with intense DWDM classical channels. N. J. Phys. 17, 043027 (2015).
Huang, D. et al. Field demonstration of a continuous-variable quantum key distribution network. Opt. Lett. 41, 3511–3514 (2016).
Karinou, F. et al. Experimental evaluation of the impairments on a QKD system in a 20-channel WDM co-existence scheme. In 2017 IEEE Photonics Society Summer Topical Meeting Series (SUM), 145–146 (IEEE, 2017).
Karinou, F. et al. Toward the integration of CV quantum key distribution in deployed optical networks. IEEE Photonics Technol. Lett. 30, 650–653 (2018).
Eriksson, T. A. et al. Coexistence of continuous variable quantum key distribution and 7 × 12.5 Gbit/s classical channels. In 2018 IEEE Photonics Society Summer Topical Meeting Series (SUM), 71–72 (IEEE, 2018).
Eriksson, T. A. et al. Wavelength division multiplexing of continuous variable quantum key distribution and 18.3 Tbit/s data channels. Commun. Phys. 2, 1–8 (2019).
Grosshans, F. et al. Quantum key distribution using gaussian-modulated coherent states. Nature 421, 238–241 (2003).
Weedbrook, C. et al. Quantum cryptography without switching. Phys. Rev. Lett. 93, 170504 (2004).
Diamanti, E. & Leverrier, A. Distributing secret keys with quantum continuous variables: principle, security and implementations. Entropy 17, 6072–6092 (2015).
Laudenbach, F. et al. Continuous-variable quantum key distribution with gaussian modulation – the theory of practical implementations. Adv. Quantum Technol. 1, 1800011 (2018).
Navascués, M., Grosshans, F. & Acin, A. Optimality of gaussian attacks in continuous-variable quantum cryptography. Phys. Rev. Lett. 97, 190502 (2006).
García-Patrón, R. & Cerf, N. J. Unconditional optimality of gaussian attacks against continuous-variable quantum key distribution. Phys. Rev. Lett. 97, 190503 (2006).
Leverrier, A. Security of continuous-variable quantum key distribution via a gaussian de Finetti reduction. Phys. Rev. Lett. 118, 200501 (2017).
Jouguet, P., Kunz-Jacques, S., Diamanti, E. & Leverrier, A. Analysis of imperfections in practical continuous-variable quantum key distribution. Phys. Rev. A 86, 032309 (2012).
Kaur, E., Guha, S. & Wilde, M. M. Asymptotic security of discrete-modulation protocols for continuous-variable quantum key distribution. Preprint at https://arxiv.org/abs/1901.10099 (2019).
Silberhorn, C., Ralph, T. C., Lütkenhaus, N. & Leuchs, G. Continuous variable quantum cryptography: Beating the 3 dB loss limit. Phys. Rev. Lett. 89, 167901 (2002).
Hirano, T., Yamanaka, H., Ashikaga, M., Konishi, T. & Namiki, R. Quantum cryptography using pulsed homodyne detection. Phys. Rev. A 68, 042331 (2003).
Leverrier, A. & Grangier, P. Unconditional security proof of long-distance continuous-variable quantum key distribution with discrete modulation. Phys. Rev. Lett. 102, 180504 (2009).
Leverrier, A. & Grangier, P. Erratum: Unconditional security proof of long-distance continuous-variable quantum key distribution with discrete modulation. Phys. Rev. Lett. 106, 259902 (2011).
Zhao, Y.-B., Heid, M., Rigas, J. & Lütkenhaus, N. Asymptotic security of binary modulated continuous-variable quantum key distribution under collective attacks. Phys. Rev. A 79, 012307 (2009).
Brádler, K. & Weedbrook, C. Security proof of continuous-variable quantum key distribution using three coherent states. Phys. Rev. A 97, 022310 (2018).
Lin, J., Upadhyaya, T. & Lütkenhaus, N. Asymptotic security analysis of discrete-modulated continuous-variable quantum key distribution. Phys. Rev. X 9, 041064 (2019).
Ghorai, S., Grangier, P., Diamanti, E. & Leverrier, A. Asymptotic security of continuous-variable quantum key distribution with a discrete modulation. Phys. Rev. X 9, 021059 (2019).
Papanastasiou, P. & Pirandola, S. Continuous-variable quantum cryptography with discrete alphabets: Composable security under collective gaussian attacks. Preprint at https://arxiv.org/abs/1912.11418 (2019).
Samsonov, E. et al. Subcarrier wave continuous variable quantum key distribution with discrete modulation: mathematical model and finite-key analysis. Sci. Rep. 10, 1–9 (2020).
Tamaki, K., Koashi, M. & Imoto, N. Unconditionally secure key distribution based on two nonorthogonal states. Phys. Rev. Lett. 90, 167904 (2003).
Koashi, M. Unconditional security of coherent-state quantum key distribution with a strong phase-reference pulse. Phys. Rev. Lett. 93, 120501 (2004).
Shor, P. W. & Preskill, J. Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 85, 441 (2000).
Lo, H. K. & Chau, H. F. Unconditional security of quantum key distribution over arbitrarily long distances. Science 283, 2050–2056 (1999).
Chabaud, U., Douce, T., Grosshans, F., Kashefi, E. & Markham, D. Building trust for continuous variable quantum states. Preprint at https://arxiv.org/abs/1905.12700 (2019).
Hayashi, M. & Tsurumaru, T. Concise and tight security analysis of the Bennett-Brassard 1984 protocol with finite key lengths. N. J. Phys. 14, 093014 (2012).
Koashi, M. Simple security proof of quantum key distribution based on complementarity. N. J. Phys. 11, 045018 (2009).
Azuma, K. Weighted sums of certain dependent random variables. Tohoku Math. J. 19, 357–367 (1967).
Namiki, R. & Hirano, T. Practical limitation for continuous-variable quantum cryptography using coherent states. Phys. Rev. Lett. 92, 117901 (2004).
Hirano, T. et al. Implementation of continuous-variable quantum key distribution with discrete modulation. Quantum Sci. Technol. 2, 024010 (2017).
Diamond, S. & Boyd, S. CVXPY: A Python-embedded modeling language for convex optimization. J. Mach. Learn. Res. 17, 1–5 (2016).
Agrawal, A., Verschueren, R., Diamond, S. & Boyd, S. A rewriting system for convex optimization problems. J. Control Decis. 5, 42–60 (2018).
Jouguet, P., Kunz-Jacques, S., Leverrier, A., Grangier, P. & Diamanti, E. Experimental demonstration of long-distance continuous-variable quantum key distribution. Nat. Photonics 7, 378–381 (2013).
Devetak, I. & Winter, A. Distillation of secret key and entanglement from quantum states. Proc. R. Soc. A: Math., Phys. Eng. Sci. 461, 207–235 (2005).
Abramowitz, M. & Stegun, I. A. Handbook of Mathematical Functions With Formulas, Graphs, and Mathematical Tables, vol. 55 (US Government printing office, 1948).
Müller-Quade, J. & Renner, R. Composability in quantum cryptography. N. J. Phys. 11, 085006 (2009).
Matsuura, T., Sasaki, T. & Koashi, M. Refined security proof of the round-robin differential-phase-shift quantum key distribution and its improved performance in the finite-sized case. Phys. Rev. A 99, 042303 (2019).
Raginsky, M. & Sason, I. Concentration of measure inequalities in information theory, communications, and coding. Found. Trends Commun. Inf. Theory 10, 1–246 (2013).
McDiarmid, C.Concentration, 195–248. Probabilistic methods for algorithmic discrete mathematics (Springer, 1998).
Carter, J. L. & Wegman, M. N. Universal classes of hash functions. J. Comput. Syst. Sci. 18, 143–154 (1979).
Pirandola, S., Laurenza, R., Ottaviani, C. & Banchi, L. Fundamental limits of repeaterless quantum communications. Nat. Commun. 8, 1–15 (2017).
Acknowledgements
This work was supported by Cross-ministerial Strategic Innovation Promotion Program (SIP) (Council for Science, Technology and Innovation (CSTI)); CREST (Japan Science and Technology Agency) JPMJCR1671; JSPS KAKENHI Grant Number JP18K13469.
Author information
Authors and Affiliations
Contributions
T.M., K.M., T.S. and M.K. contributed to the initial conception of the ideas, to the working out of details, and to the writing and editing of the manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Peer review information Nature Communications thanks Anthony Leverrier and the other, anonymous, reviewer(s) for their contribution to the peer review of this work. Peer reviewer reports are available.
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons license, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons license and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this license, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Matsuura, T., Maeda, K., Sasaki, T. et al. Finite-size security of continuous-variable quantum key distribution with digital signal processing. Nat Commun 12, 252 (2021). https://doi.org/10.1038/s41467-020-19916-1
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41467-020-19916-1
This article is cited by
-
Continuous-mode quantum key distribution with digital signal processing
npj Quantum Information (2023)
-
Hardware design and implementation of high-speed multidimensional reconciliation sender module in continuous-variable quantum key distribution
Quantum Information Processing (2023)
-
Practical continuous-variable quantum key distribution with composable security
Nature Communications (2022)
-
Neural network-based prediction of the secret-key rate of quantum key distribution
Scientific Reports (2022)
Comments
By submitting a comment you agree to abide by our Terms and Community Guidelines. If you find something abusive or that does not comply with our terms or guidelines please flag it as inappropriate.